This September, the ARCADIAN-IoT Summer School will open its doors in Stockholm to offer PhD students and young researchers an in-depth exploration of the ever-evolving landscape of IoT cybersecurity.
IoT Cybersecurity: Tackling Challenges and Opportunities
4 – 8 September 2023
Stockholm, Sweden @RISE – Research Institute of Sweden
NEW: The registration deadline has been extended to 31 July 2023
The PhD Summer School on IoT Cybersecurity is aimed at PhD students and young researchers in the field of computer science and engineering. The goal of the summer school is to provide participants with a comprehensive understanding of the challenges and opportunities in the field of IoT cybersecurity and to equip them with the knowledge and skills required to tackle current and future security challenges in IoT.
The school will cover a wide range of topics related to IoT cybersecurity, including IoT architecture and protocols, security challenges in IoT, privacy and security in IoT, security mechanisms in IoT, security in cloud-based IoT, and emerging trends in IoT cybersecurity. The lectures will be delivered by renowned experts in the field of IoT cybersecurity and will provide participants with an opportunity to learn about the latest research, developments, and best practices in the field.
The school will provide a platform for participants to network with international experts, exchange ideas and knowledge, and also the opportunity to present their own research and receive feedback and guidance.
All participants of the school will receive an official attendance certificate upon the completion of the school. Furthermore, by actively participating in the entire week of the school and submitting a report that showcases their own findings and key insights from the topics covered, students will have the opportunity to earn 3 ECTS credits.
The school is offered free of charge to all participants. All costs, including lunches and coffee breaks, will be fully covered by the ARCADIAN-IoT project.
Organised by:




The school is free of charge. The school is primarily aimed at PhD students; however, we also welcome registrations from young researchers who have obtained their PhD degree within the last two years. Attendees should be either working in the cybersecurity domain or adjacent areas to ensure maximum relevance and value of the knowledge shared during the event.
The registration deadline is 31 July 2023 25 August 2023.*
Please note that we have a limited capacity of attendees, registration forms should be submitted as early as possible, as the students will be prioritized on a first come first served basis.
To apply to the School, please fill out this form and send it to [email protected]
Once you have submitted your registration form, our team will review your data before confirming the successful registration. If all looks good, you will receive an email from us requesting proof of your flight/train reservation that must be provided within 5 calendar days. Failure to do so will result in your registration being cancelled and your priority being given to the next person on the list.**
If we have already reached the maximum number of participants, new requests of registration will be put on hold in case of any spot gets available.
If you have any questions, please send an email to: [email protected]
* If you are not a PhD student or young researcher, we welcome you to send us an email with a motivation letter explaining why you would like to take part. We will revise your request and get back to you.
** Students living in Stockholm or in the surrounding areas are exempt from providing proof of reservation.
CONFIRMED SPEAKERS

Andrei Sabelfeld

Maria Eichlseder

Shahid Raza

Kai Rannenberg

Mauro Conti

Nicolas Tsiftes

Joakim Eriksson
Jonghoon Kwon

João Casal

Marco Tiloca
![Foto_arancio[70] copy Foto_arancio[70] copy](/wp-content/uploads/sites/76/2023/08/Foto_arancio70-copy.png)
Antonio Lioy
Antonio Lioy holds a MSc in Electronic Engineering and a PhD in Computer Engineering. He is Full Professor of cybersecurity at the Politecnico di Torino, Italy, where he leads the TORSEC research group. Since 1996, he has taken part to more than 20 European research projects in the cybersecurity area and published more than 100 research papers.

Andreas Kurth

Sérgio Figueiredo
Stewart Kowalski
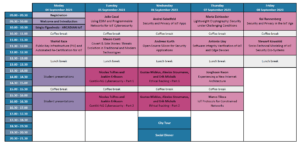
Program
Monday, 4 September |
|
| 09.00 – 09.30 | Registration |
| 09.30 – 10.00 | Welcome and Introduction Alfonso Iacovazzi, RISE Research Institutes of Sweden |
| 10.00 – 10.30 | Introduction to the ARCADIAN-IoT project Sérgio Figueiredo, Instituto Pedro Nunes |
| 10.30 – 11.00 | Coffee break |
| 11.00 – 12.30 | Public Key Infrastructure (PKI) and Automated Re-Certification for IoT Shahid Raza, RISE Research Institutes of Sweden Asymmetric cryptography has long been considered infeasible for resource-constrained devices. However, since the new IoT devices are equipped with sufficient RAM, flash, a standard 32-bit CPU and crypto hardware it is possible to bring internet-grade security to IoT. This talk will present PKI building blocks for resource-constrained IoT devices and highlight current standardization efforts around this. However, availability of security protocols is not enough, it is also important that IoT manufacture must enable and continuously test state-of-the-art security solutions, which is covered by the new EU Cybersecurity Act though cybersecurity certification. Traditional methods for one-off and manual certification are not scalable to millions of heterogeneous IoT devices. This is particularly important when regular software updates are necessary, which may break the certificate seal. It is therefore necessary that automated, lightweight, and cost-effective initial- and re- certification techniques should be available for modern IoT devices. This talk will also present such an automated re-certification solution for IoT and its integration with state-of-the-art standardized security solutions for IoT devices. |
| 12.30 – 13.30 | Lunch break |
| 13.30 – 15.00 | Student presentations |
| 15.00 – 15.30 | Coffee break |
| 15.30 – 17.00 | Student presentations |
Tuesday, 5 September |
|
| 09.00 – 10.30 | Using ESIM and Programmable Networks for IoT Cybersecurity João Casal, Truphone With the rise of devices connected to the internet, increasing the robustness of security frameworks for IoT is an urgent demand. In this sense, SIMs are ubiquitous technologies used for over 30 years for security processes (e.g subscriber identification and authentication in cellular networks). Extending the security features of those well-accepted secure elements for IoT seems like a natural step. Furthermore, the programmatic control of network functions according to security knowledge and needs is quite promising – these functions are positioned between the devices and the internet and have ability to control communications. This keynote will focus on these 2 aspects: the use of eSIM and of Programmable Networks for IoT cybersecurity. |
| 10.30 – 11.00 | Coffee break |
| 11.00 – 12.30 | Covert & Side Stories: Threats Evolution in Traditional and Modern Technologies Mauro Conti, University of Padua Alongside traditional Information and Communication Technologies, more recent ones like Smartphones and IoT devices also became pervasive. Furthermore, all technologies manage an increasing amount of confidential data. The concern of protecting these data is not only related to an adversary gaining physical or remote control of a victim device through traditional attacks, but also to what extent an adversary without the above capabilities can infer or steal information through side and covert channels! In this talk, we survey a corpus of representative research results published in the domain of side and covert channels, ranging from TIFS 2016 to more recent Usenix Security 2022, and including several demonstrations at Black Hat Hacking Conferences. We discuss threats coming from contextual information and to which extent it is feasible to infer very specific information. In particular, we discuss attacks like inferring actions that a user is doing on mobile apps, by eavesdropping their encrypted network traffic, identifying the presence of a specific user within a network through analysis of energy consumption, or inferring information (also key one like passwords and PINs) through timing, acoustic, or video information. |
| 12.30 – 13.30 | Lunch break |
| 13.30 – 15.00 | Contiki-NG Cybersecurity – Part 1 Nicolas Tsiftes and Joakim Eriksson, RISE Research Institutes of Sweden This tutorial provides an overview of cybersecurity features in Contiki-NG, an open-source operating system for resource-constrained IoT devices. The tutorial contains both presentations and hands-on exercises covering two main topics: secure connectivity and trusted execution environments. First, we will show the participants how to set up an application with secure connectivity using CoAP and DTLS. Second, we will show how to use Arm TrustZone in Contiki-NG. During the exercises, the participants will get the opportunity to work with both the Cooja simulator and a real IoT platform (Nordic Semiconductor nRF5340), and use a Docker-based development environment. Through this tutorial, participants will gain practical experience of using Contiki-NG’s cybersecurity features in a resource-constrained IoT environment. |
| 15.00 – 15.30 | Coffee break |
| 15.30 – 17.00 | Contiki-NG Cybersecurity – Part 2 Nicolas Tsiftes and Joakim Eriksson, RISE Research Institutes of Sweden |
Wednesday, 6 September |
|
| 09.00 – 10.30 | Security and Privacy of IoT Apps Andrei Sabelfeld, Chalmers University IoT apps empower users by connecting a variety of otherwise unconnected services. IoT apps often run on Trigger-Action Platforms (TAPs) that receive app input from trigger services and send app output to action services. With the convenience and interoperability of TAPs comes the concern that the TAP is effectively a “person-in-the-middle”, acting on behalf of the user with respect to trigger and action services. This poses security and privacy challenges since in the event of a compromised TAP, the users’ sensitive input data is also compromised. We demonstrate that popular TAPs are susceptible to several classes of attacks that violate user privacy, integrity, and availability. We suggest countermeasures, discuss the formal guarantees they provide, and evaluate their effectiveness on practical benchmarks. Finally, we discuss how data access minimization can be enforced automatically on TAPs so that excessive amounts of sensitive data is not sent to the TAPs in the first place. |
| 10.30 – 11.00 | Coffee break |
| 11.00 – 12.30 | Open-Source Silicon for Security Applications Andreas Kurth, lowRISC “Don’t roll your own crypto” is a widely quoted mantra in the software industry, and for most purposes best practice is to use well established open-source libraries instead. In the silicon (integrated circuits) industry, however, open source is much less prevalent, even though it has many benefits especially for security technology: it enables transparency and auditability by independent parties, and it makes canonical, scrutinized implementations of key components a commodity. In this talk, we discuss challenges with open source and security that are unique to silicon and present four key security components that are available as open-source silicon today: a block cipher (AES) accelerator, a message authentication code / hashing (Keccak/SHA3) accelerator, a RISC-V CPU core, and a root of trust (RoT) combining the former three. |
| 12.30 – 13.30 | Lunch break |
| 13.30 – 15.00 | Ethical hacking – Part 1 Gustav Midéus, Alexios Stournaras, and Erik Mickols, RISE Research Institutes of Sweden This session will provide an introduction to the world of hacking. You will get familiar with some of the techniques and approaches used in real hacking scenarios and get experience trying to break the security of computer software. We will begin with an introduction on some of the central concepts and techniques within the field and then move on to a practical exercise where you will get the opportunity to try your skills and knowledge to solve a number of hacking challenges. Working as a team you will get to participate in a small scale Capture the Flag (CTF) competition where the goal is to identify and exploit a number of software vulnerabilities in order to find hidden messages (flags). Our goal is to open your eyes to the practical side of cybersecurity and give you a better understanding of how hacking works in practice. |
| 15.00 – 15.30 | Coffee break |
| 15.30 – 17.00 | Ethical hacking – Part 2 Gustav Midéus, Alexios Stournaras, and Erik Mickols, RISE Research Institutes of Sweden |
| 17.30 – 19.00 | City Tour |
| 19.30 – 21.30 |
Social Dinner @ TRE VALV – Järntorget 83, 111 29 Stockholm |
Thursday, 7 September |
|
| 09.00 – 10.30 | Lightweight Cryptography: Security under Challenging Conditions Maria Eichlseder, Graz University of Technology Integrating cryptographic algorithms in IoT systems and other constrained environments is often difficult due to limited resources and additional security challenges. Driven by this demand, NIST has initiated a lightweight cryptography competition between 2019 and 2023. Among 57 submissions, Ascon has been selected as the new standard for authenticated encryption and hashing. In this talk, we show how Ascon was designed to address the specific challenges in the IoT, including security, performance, and footprint. Since ciphers are not used in an ideal world, we show how Ascon also improves robustness against certain implementation attacks and mistakes. |
| 10.30 – 11.00 | Coffee break |
| 11.00 – 12.30 | Software Integrity Verification of IoT and Edge Devices Antonio Lioy, Politecnico di Torino IoT and edge devices are prone to easy software manipulation due to their physical distribution and low-cost, which often implies low security standards. Trusted computing techniques may help to demonstrate the software integrity of a node, as well as its real identity. This talk will introduce concepts about hardware root-of-trust, trusted execution, remote attestation, and device identity, showing how they can cooperate to provide better security in nodes with limited computational resources, such as IoT and edge devices. Finally, the implementation of this approach foreseen by the SPIRS project will be described. |
| 12.30 – 13.30 | Lunch break |
| 13.30 – 15.00 | Experiencing a New Internet Architecture Jonghoon Kwon, ETH Zürich Imagining a new Internet architecture enables us to explore new networking concepts without the constraints imposed by the current infrastructure. What are the benefits of a multi-path inter-domain routing protocol that finds dozens of paths? What about a data plane without inter-domain forwarding tables on border routers? What secure systems can we build if a router can derive a symmetric key for any host on the Internet within nanoseconds? In this presentation, we invite you to join us on our 13-year long expedition of creating the SCION next-generation secure Internet architecture. SCION has already been deployed at several ISPs and domains, and has been in production use since 2017. On our journey, we have found that path-aware networking and multipath communication not only provide security benefits, but also enable higher efficiency for communication, increase network capacity, and can even provide opportunities for reducing the carbon footprint of communication. |
| 15.00 – 15.30 | Coffee break |
| 15.30 – 17.00 | IoT Protocols for Constrained Networks Marco Tiloca, RISE Research Institutes of Sweden This seminar overviews recent research and standardization activities on lightweight solutions for end-to-end secure (group) communication, as especially suitable for the Internet of Things (IoT). First, we will introduce the IETF standards CoAP and OSCORE as main building blocks for message exchange and end-to-end security. Then, we will consider methods for establishing and updating keying material for OSCORE. After that, we will focus on the adaptation of OSCORE to support secure group communication in CoAP groups. This will cover message protection with the Group OSCORE security protocol; the secure provisioning of group keying material leveraging the ACE framework for access control; as well as advanced communication models and supportive management services for secure group communication. The presented topics will be positioned in the remit of the related standardization activities within the Internet Engineering Task Force (IETF). |
Friday, 8 September |
|
| 09.00 – 10.30 | Security and Privacy in the IoT Age Kai Rannenberg, Goethe University Frankfurt Within the “Internet of Things” paradigm connected devices are covering more and more aspects of personal activities, business processes and public life, e.g. in household assistance, smart manufacturing (Industry 4.0) and traffic. Often safety critical processes like controlling vehicles and critical infrastructures are involved and very sensitive data are being processed. These developments ask for attention to security and privacy aspects, which often are not understood by all players. This talk will discuss some examples of the Internet of Things and the respective security and privacy issues. Where appropriate it will give hints to technical, organisational, regulatory or strategic trends and solution approaches and/or the lack thereof. |
| 10.30 – 11.00 | Coffee break |
| 11.00 – 12.30 |
Socio-Technical Modeling of IoT Security Eco-Systems Stewart Kowalski, Norwegian University of Science and Technology |
| 12.30 – 13.30 | Lunch break |
The ARCADIAN-IoT Summer School will take place in person at RISE – Drottning Kristinas väg 61, 114 28 Stockholm.
- Arlanda Express train: Fast & eco-friendly between Airport & Stockholm Central Station. No stops, 20 min to Centre. Leaves every 15 min. The round-trip ticket costs 600 SEK. Buy tickets at airport/central station or online: www.arlandaexpress.com. From Central Station, take metro red line nr 14 towards Mörby centrum, get off at Tekniska Högskolan (KTH).
- Airport coaches: 40 minutes to Centre. Leaves every 5-10. The round-trip ticket costs 209-239 SEK. Buy tickets at the airport/City terminal or via the Airport coaches’ app. From City terminal, walk to Central Station and take metro red line nr 14 towards Mörby centrum, get off at Tekniska Högskolan (KTH). For more information, visit www.flygbussarna.se/en.
- Stockholm Public Transport (SL): Commuter trains between Uppsala and Stockholm. 40 min to the centre. Every 15 min. Visit www.sl.se/en for details. There is a fee of 132 SEK for passing between the train and the airport terminal at Arlanda. From Central Station, take metro red line nr 14 towards Mörby centrum, get off at Tekniska Högskolan (KTH).
- Taxi: Make sure to choose a properly certified company such as
- Taxi Stockholm: + 46 (0) 8 15 00 00
- Sverige Taxi: + 46 (0) 20 20 20 20
- Taxi Kurir: +46 (0) 771 86 00 00
- Uber is also available in Stockholm.
- Metro: Take red line nr 14 towards Mörby centrum and get off at Tekniska Högskolan (KTH).
Organizing Committee:
- Shahid Raza
- Alfonso Iacovazzi
- Sérgio Figueiredo
Publicity Chair:
- Valentin Popescu
For further information please send an email to the ARCADIAN-IoT Summer School organising committee: [email protected]
We have made arrangements with Elite Hotel Arcadia to offer our students accommodation at a fixed price (1372 SEK/per night). Due to limited availability, we encourage you to make your reservation as soon as possible.
The last day to book a room is on 12 August.
The reservation can be canceled free of charge until 7 days before arrival.