Mobile technology has facilitated the proliferation of connected devices, the so-called Internet of Things (IoT) across many sectors from smart cities, to telehealth, industry and beyond. The prevalent identity management for IoT Devices today include centralized identity management, X.509 certificates, shared secret and also simple userId & password solutions[1]. These identity management solutions suffer from known security vulnerabilities, privacy concerns and scalability issues.
The mobile industry is now working on the sixth generation of cellular network technology 6G[2] which is being touted to revolutionize the way we connect and interact over virtual reality, sensory and telehealth IoT Devices, voice-controlled AI assistants, Autonomous Vehicles etc.
6G´s primary goal is to provide this necessary bandwidth and low latency technology for real-time data exchange to facilitate this new era.
However, as traditional centralized identity and certificate-based management systems have known limitations and are not the best fit to handle the exponential growth of IoT devices and their greater penetration into our personal lives, that require ever more scalable, secure and privacy preserving identity solutions. Self-Sovereign Identity (SSI) and Decentralized Identifiers (DIDs) have emerged as promising technologies, building on the principles of Zero Trust[3](never trust, always verify, least privilege, etc., to address these challenges.
This paper explores in more detail these technologies so to facilitate 6G use cases with State-of-the-Art secure and scalable decentralized and distributed identity management for IoT devices, systems and the end users that rely on them.
SSI is a decentralized approach to identity management that gives individuals and organizations control over their own identities. In an SSI system, individuals own and manage their own identities in mobile or web wallets, which store Verifiable Credentials issued by trusted parties to attest such things as national eID, drivers license, employee ID etc. just like a real wallet holds such physical ID cards. Cryptographic technology is used to sign the Verifiable Credentials so to prove that they were issued by a trusted organization or presented by a specific end user´s wallet. This cryptographic information is associated with Decentralized Identifiers (DIDs) managed by end user´s and organizations themselves rather than Certificate Authorities in the case of X.509 certificates.
In the case of EBSI (European Blockchain Services Infrastructure[4]), Issuers DIDs are published on a decentralized blockchain, where the EBSI ledger contains the cryptographic material associated to the Issuer´s DID that is used by verifiers to check it is an authentic credential. This ensures trust is ensured by one well known trusted organization in a decentralized and highly scalable approach provided by the distributed ledger technology. This is illustrated in the following EBSI Issuer Trust Model[5] figure.
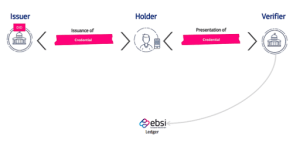
To prove their identity to others, individuals can create verifiable credentials (VCs) that are issued by trusted parties. VCs are cryptographically secure documents that contain information about an individual’s identity, such as their name, date of birth, and education. When an individual presents a VC to a verifier, the verifier can verify the VC’s authenticity and the information it contains.
In ARCADIAN-IoT project[6] various DIDs were used depending on the scenario, e.g. DID:PEER[7] privacy preserving DID for mobile wallets, DID:WEB[8] for Issuers and constrained devices and DID:PRIV[9] for IoT Devices. These were deployed and proven with SSI authentication for various domain pilots such as Drones (M2M use cases) and their users, Patients and Medical Professionals (P2M use cases).
In the case of IoT Devices that have sufficient resources to support cryptographic operations, an SSI Agent is able to be deployed on the device and integrated with the business logic to support ZTP making use of the device fingerprint to be issued as a Verifiable Credential by a trusted security framework, which is later used for authentication purposes. The figure below demonstrates the use of SSI in this approach used in the ARCADIAN-IoT project.
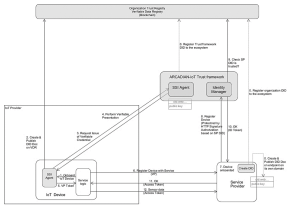
This approach followed a secure ZTP approach with the device generating its own DID on a permissioned blockchain, which only members of ecosystem can access, and identity claims based on its device fingerprint, were issued to the IoT Devices as a Verifiable Credential.
However, constrained IoT devices in ARCADIAN-IoT do not contain enough processing power to perform the necessary cryptography signing operations. Therefore, the solution devised was for an IoT GW platform to handle the DID authentication on behalf of the constrained IoT Devices with DID challenge / response towards the ARCADIAN-IoT trusted framework for authorising token-based access to Service Provider systems. The IoT Device used a shared secret for authentication with the IoT GW. This approach taken in ARCADIAN-IoT for constrained IoT Devices is shown below in the following figure.
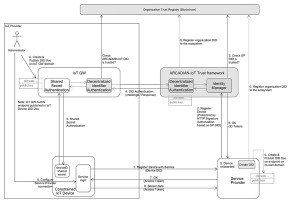
From the above figure, we can see that the IoT Device itself does not support an SSI agent and this is because it lacks sufficient resources to support the public private key cryptographic signing of Verifiable Credentials. Considering the aims of 6G, include to support increased bandwidth and for ever more constrained IoT Devices it would be advantageous that SSI agents make use of the cryptographic capabilities of eSIM deployed with IoT Devices.
Therefore, it is concluded that a key area for further exploration in the convergence of 6G with SSI and Decentralized Identifiers is to provide guidelines on the cryptographic signing algorithms implementation on eSIM’s for handling the signing of verifiable presentation for IoT Devices and to align with EBSI guidelines to achieve greater interoperability. This will bring an extra level of public private crypto security, zero touch provisioning and lifecycle management capabilities that is not currently available for constrained devices.
Considering the P2M interoperability achieved by EBSI in Europe on establishing integration guidelines[10] and certification of compliant mobile wallets[11], then this is an important area that is needed to promote the M2M interoperability and 6G standardisations should consider collaboration with EBSI to ensure wider SSI interoperability amongst IoT Device vendors.
____________________________________
[1] Landscape of IoT security, Eryk Schiller, Andy Aidoo, Jara Fuhrer, Jonathan Stahl, Michael Ziörjen, Burkhard Stiller
[2] https://www.etsi.org/newsroom/news/2307-3gpp-commits-to-develop-6g-specifications#:~:text=3GPP%20has%20developed%20international%20standards,of%206G%20global%20harmonized%20standards.%22&text=%22Success%20is%20something%20that%20we%20must%20work%20to%20maintain.
[3] https://trustoverip.org/blog/2022/02/22/no-i-dont-trust-you-implementing-zero-trust-architecture-in-the-world-of-self-sovereign-identity-ssi/
[4] https://ec.europa.eu/digital-building-blocks/sites/display/EBSI/Home
[5] https://ec.europa.eu/digital-building-blocks/wikis/download/attachments/597952490/Chapter%205%20-%20Issuer%20Trust%20Model%20.pdf?version=1&modificationDate=1666602514393&api=v2#:~:text=Trusted%20Issuer%20(TI)%20is%20responsible,it%20manages%20a%20DID%20document.
[7] GitHub – decentralized-identity/peer-did-method-spec: A rich DID method that has no blockchain dependencies. The verifiable data registry is a synchronization protocol between peers.
[8] https://w3c-ccg.github.io/did-method-web/
[9] Private DID method implemented on Hyperledger Fabric Permissioned Blockchain in ARCADIAN-IoT Project

